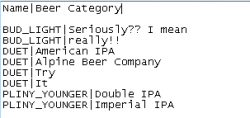
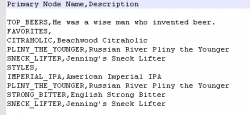
Fun with Oracle DRM and JavaScript

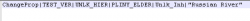
Episode 1: PropDefObject Good day all! I thought I would start a new blog series detailing the different (Oracle DRM) Data Relationship Objects and how to work with them using the newer JavaScript option available for derived property types. In this first episode, we will look at the PropDefObject object since I recently worked with……